EDG Integration with Hashicorp Vault
Install and configure Hashicorp Vault:
Ensure the listener is using TLS
Enable the key-value secrets engine
Create an ACL policy called “edg”:
path "kv/data/edg/secure-storage/*" { capabilities = [ "create", "read", "update", "delete" ] } path "kv/metadata/edg/secure-storage" { capabilities = [ "list" ] }Enable the AppRole auth method
Create an approle called “edg” that uses the edg policy:
vault write auth/approle/role/edg token_policies="edg" token_ttl=1h token_max_ttl=4h
Get the role-id for the edg approle:
vault read auth/approle/role/edg/role-id
Generate a secret-id for the edg approle:
vault write -force auth/approle/role/edg/secret-id
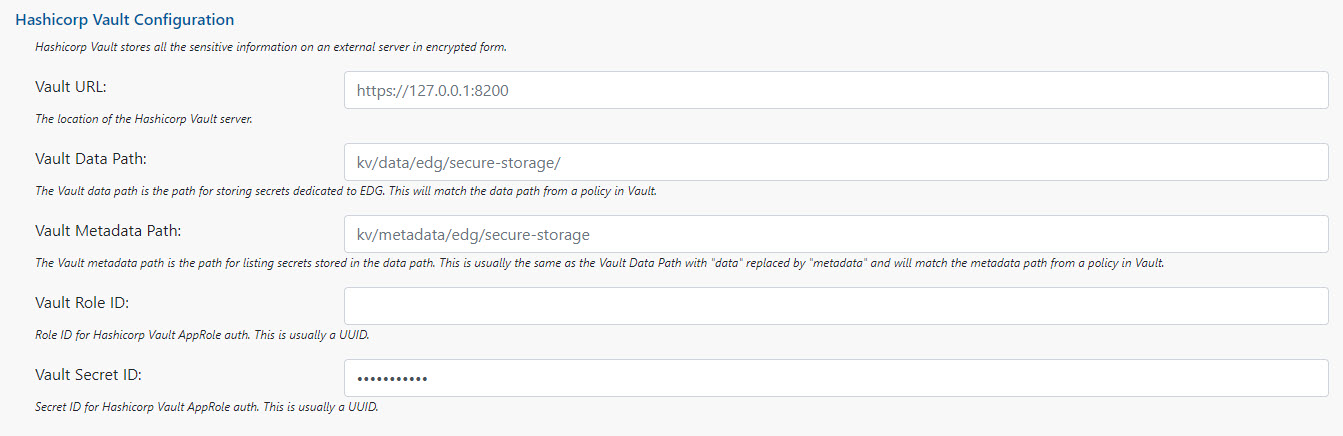
Enter the vault type and vault URL into EDG setup configuration:
vaultType = Hashicorp hashicorpVaultURL = https://127.0.0.1:8200
Enter the data path and metadata path (from the edg policy) into EDG configuration:
hashicorpVaultDataPath = kv/data/edg/secure-storage/ hashicorpVaultMetadataPath = kv/metadata/edg/secure-storage
Enter the role-id and secret-id into EDG setup configuration:
hashicorpVaultRoleId = <role-id> hashicorpVaultSecretId = <secret-id>
If using interactive setup, steps 8 through 10 are done on the Interactive Setup UI